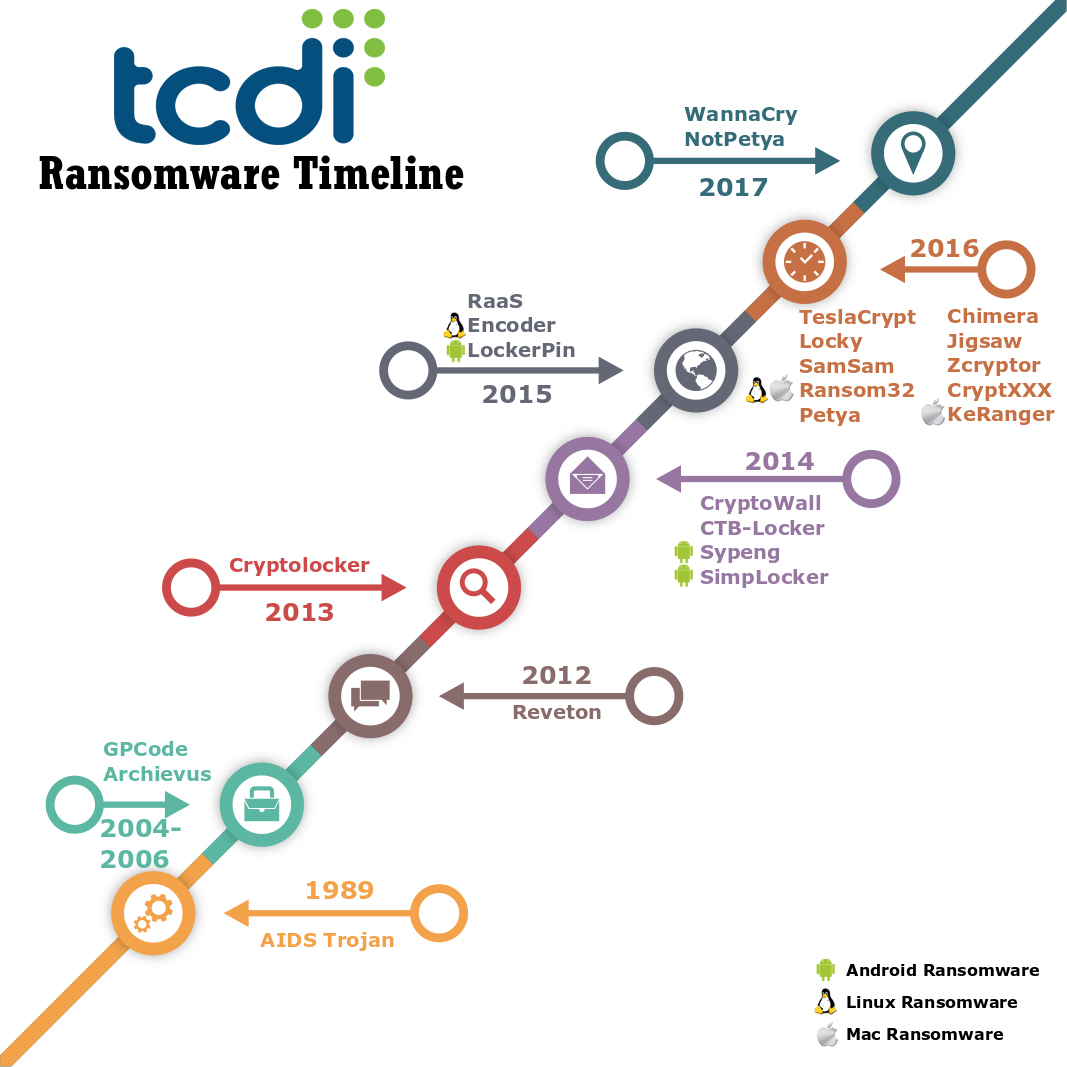
 Ransomware, the malicious code that holds so much data captive, is now more commonplace than data breaches. It continues to be a thorn in the side of companies large and small, and it has enriched many cyber criminals in the course of its history. It targets computers, mobile devices, and even IoT.
Ransomware, the malicious code that holds so much data captive, is now more commonplace than data breaches. It continues to be a thorn in the side of companies large and small, and it has enriched many cyber criminals in the course of its history. It targets computers, mobile devices, and even IoT.
The ransomware we know today is predominantly crypto-ransomware. This ransomware utilizes encryption to hold data hostage until a ransom is paid. Other current ransomware includes locker ransomware which prevents users from accessing their devices; ransomware hoaxes which claim to encrypt data when they haven’t; advanced ransomware threats (link to previous article), highly specialized attacks of an organization designed to do the most damage; and destructive ransomware which encrypts or deletes data with no capability to restore it.
So how did we come to be in this situation?
Flashback to 1989
The idea of ransomware was conceptualized in 1989 with the AIDS Trojan. This ransomware was distributed on a 5 ¼” floppy disk that was mailed to victims. It contained a program that surveyed victims to determine their likelihood of contracting AIDS. At the same time, the program encrypted the victim’s hard drive and then printed a ransom demand of $189. The author of the AIDS Trojan was found and further disks were not mailed out.
This ransomware was unique and not replicated for many years. The AIDS Trojan was distributed during an era of much experimentation in malicious code and cyber-attacks with little monetization of these techniques occurring due to the limited ability of lone hackers and small groups to launder money or hide their tracks effectively.
Over the years, some hacking groups targeted specific companies with hacks that stole data, which they then ransomed back to their victims, but none of these attacks automated the process as the AIDS Trojan did. The concept of ransomware would slumber until it was awakened in 2004.
2004
The GPCode ransomware encrypted files on Windows machines with a custom encryption algorithm. Ransom messages were delivered in a text file on the victim’s desktop stating that their files could be decrypted with the purchase of a decryption program. Fortunately, the custom encryption algorithm used by GPCode was easy for analysts to crack.
2006
In 2006 the Archievus ransomware appeared on Windows computers. Archievus encrypted the contents of the My Documents folder using RSA asymmetric encryption. The ransomware demanded that victims make purchases from certain websites to receive the decryption key. The designer of Archievus used the same decryption key for all infections. Once this was realized and published, Archievus’s ransom demands became useless.
In the same year, the Trojan.Ransom.A was distributed. This locking Trojan placed itself in the Windows startup so that a message is displayed on the screen along with pornographic images. The ransom note covered the entire screen, preventing the victim from clicking anywhere else. Trojan.Ransom.A demanded payment with Western Union of $10.99. The CIDN number on the receipt was to be entered to remove the ransom message. However, Trojan.Ransom.A was more adware than ransomware. It modified internet settings to proxy connections and created many popups and password prompts.
2012
In 2012 saw the release of Reveton, a ransomware that pretended to be a message from the FBI notifying the victim that their computer had been locked because of copyright violations and distribution of pornographic content. It claimed that access was denied to the machine until a fine was paid. This was the first of many ransomware dubbed “police ransomware.” Reveton was distributed through compromised websites in a technique known as “drive by” where a user simply clicks on a portion of the compromised site and the ransomware is installed. Reveton demanded payment through Paysafecard or Ukash.
2013
In 2013, the world was served a cyber-bombshell named Cryptolocker. This ransomware spread through compromised websites and malicious email attachments. The creation of Bitcoin in 2009 opened up an anonymous method of extortion that had previously been unavailable to attackers. Cryptolocker used AES-256 to encrypt files and demanded payment in this new currency. It used command and control servers spread across the Zeus botnet communicating over the Tor network to distribute decryption keys.
All these techniques combined to make it much harder to track down the criminals behind it. However, Cryptolocker’s reliance on command and control servers was also its downfall when the Zeus botnet was largely demolished in 2014.
2014
The CryptoWall ransomware was heavily distributed in 2014. It produced a staggering estimated revenue of $325 million for cybercriminals. It fixed flaws in its predecessor, Cryptodefense, a ransomware that utilized 2048-bit RSA encryption but left the decryption key in plain text on the computer. Cryptowall employed exploit kits and was harder to eradicate because of its ability to copy itself into registry keys and startup folders.
CTB-Locker was also released in 2014. This ransomware deleted Windows volume shadow copies. Shadow copies track changes to files so that previous versions of a file can be retrieved. Up till this point, shadow copies had been an easy way for victims to restore their data. Victims who relied chiefly upon shadow copies as their backup method were rudely awakened to its inadequacy.
Sypeng was the first ransomware to target mobile devices. It was detected in 2014 when victims started receiving text messages that appeared to be Adobe Flash updates. These text messages contained the Sypeng ransomware that locked the victim’s Android phone or tablet, demanding $200 in MoneyPacks. Later the same year, SimpLocker attacked Android phones and encrypted them rather than just locking them out.
2015
The attack on mobile devices continued in 2015 with the release of LockerPin. This locker ransomware reset the pin of Android phones and demanded $500 to unlock the device.
A ransomware designed especially for Linux was also released in 2015. Encoder was the first ransomware to targeted Linux-based web hosting systems such as the popular Magento and cPanel. It locked web directories and encrypted the contents.
The Chimera ransomware not only encrypted files but also threatened to publish files online if ransoms were not paid in a practice known as doxing while an open source ransomware called Hidden Tear was placed in GitHub. Hidden Tear was provided ostensibly for educational purposes, but many malicious programmers snatched it up to create a host of ransomware variants.
2015 was also the year for Ransomware as a Service (RaaS). These RaaS kits allowed criminals to distribute ransomware for about $3000. In 2016, many new kits such as Petya, Mischa, Tox, Ransom32, and Cryptolocker Service entered the market making ransomware much more accessible to criminals. Increased competition brought more differentiation and reduction in price with some RaaS tools for sale as low as $39.
2016
Ransomware only continued to refine itself and it sought out additional targets. The first ransomware targeting Macs called KeRanger was released in 2016. KeRanger was distributed through a fake Transmission BitTorrent client. Another first was the release of a ransomware built on JavaScript. Ransom32 used JavaScript to infect machines running on multiple platforms including not only Windows but also Linux and Mac.
The Jigsaw ransomware taunted victims with threats to delete a file every hour until the $150 ransom demand was paid. It also claimed it would delete 1,000 files if the machine was restarted or if the ransomware process was stopped.
Ransomware also introduced features to make it easier for victims to pay ransoms. The SamSam ransomware included a live chat with victims to help guide them through the process of paying the ransom.
Petya introduced a new propagation method through cloud file sharing services. Petya used Dropbox to distribute itself. Once Petya infected machines, it proceeded to lock the machine by encrypting the MBR. Later in the year, a ransomware called Mamba encrypted the full hard drive and external or USB drives attached to the victim machine using AES-256.
ZCryptor was the first ransomware worm. It was able to distribute itself through spam email and through the network. It was capable of encrypting the local machine and shared network drives. At the same time, TeslaCrypt and Locky were used extensively by criminal enterprises to lock and extort victims. These ransomware employed techniques from a variety of other ransomware in an effective combination with strong distribution networks.
Researchers scrambled to analyze and develop countermeasures for an increasing number of ransomware titles. In response, the CryptXXX ransomware was equipped with functions to monitor for the presence of a sandbox. CryptXXX could stop its processes if it detected that it was running in a sandbox. This made it more difficult for researchers to obtain information on how it operated.
2017
WannaCry was easily the fastest spreading ransomware in history. In just four days, it had infected more than 250,000 devices using techniques from the leaked EternalBlue NSA hacking tool and an SMB protocol vulnerability. NotPetya was initially distributed with fake updates to the M.E.Doc tax software. It then used almost the same Microsoft SMB vulnerability that WannaCry used to destroy data on hundreds of thousands of machines for this version of Petya did not provide victims with recovery keys.
Today
We finally arrive at today where ransomware developers are surely working on newer, more potent ransomware. We must stay vigilant in protecting our systems and data, all the while ensuring that valuable data is effectively backed up.
________________________________________________________
This post is Part 4 of 4 of a series discussing Ransomware: Part 1: The Economics of Ransomware, Part 2: They Psychology Behind Infamous Ransomware, and Part 3: The 6 Phases of an Advanced Ransomware Threat. To learn more about what ransomware is and how it is distributed, please visit our blog post The Five W’s (and How) of Ransomware.