
Guidelines for Username and Password Risk Management
Hackers often bypass some of the best security technologies by exploiting one of the oldest tricks in the book, your password. Not only will attackers

Hackers often bypass some of the best security technologies by exploiting one of the oldest tricks in the book, your password. Not only will attackers

Briefcase chained to his wrist, the officer cautiously looks for anything out of the ordinary as he makes his way purposefully to a black vehicle
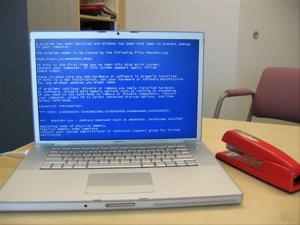
Do you think there is a right way to crash? A system crash sounds like a bad thing all around but there are safe ways

Many organizations use Cisco devices to interconnect, protect, filter, and manage networks so it is important to understand ways to improve the security of these
An information security risk assessment is the process of identifying vulnerabilities, threats, and risks associated with organizational assets and the controls that can mitigate these

Information security policies and security awareness go hand in hand. Frankly, a policy is worthless if it sits on someone’s desk. Information security policies find value