How to Develop Your Cybersecurity Strategy
When it comes to developing a cybersecurity strategy, determining where to start or what to do next is not always clear. Along with increasingly complex regulatory requirements, identifying an approach that is proportional to the needs to an organization is a common concern that we hear time and time again.
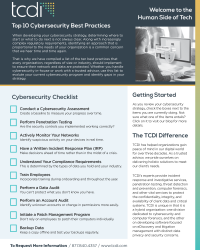
That is why we have compiled a list of the ten cybersecurity tips and best practices that every small-to-mid-sized business (SMB), regardless of size or industry, should implement to ensure their network and data are protected. Whether you handle cybersecurity in-house or work with a trusted advisor, use this list to evaluate your current cybersecurity program and identify gaps in your strategy.
Conduct a Cybersecurity Assessment
Create a baseline to measure your progress over time
The first issue that every organization needs to address is performing a cybersecurity assessment. While you can lead yourself through the Center for Internet Security Controls (CISC) checklist, best practice indicates that a third-party be brought in to evaluate your organization.
During an assessment, your security controls are reviewed against industry best practices and applicable regulatory requirements. Your trusted advisor will then analyze the results and be able to tell you what you are doing well, as well as identify areas for improvement.
Another value of a cybersecurity assessment is the baseline that is created, allowing you to track and measure your progress over time. At the conclusion of an assessment, you also receive a prioritized action plan outlining security recommendations. The priority of the list is based on risk to the organization and cost to implement. For example, high risk findings that are low cost to remediate, such as enabling multi-factor authentication or implementing encryption across company devices, will appear at the top of the list of recommendations.
Perform Penetration Testing
Are the security controls you implemented working correctly?
The next issue that needs to be addressed is penetration testing. As previously discussed, an assessment outlines what you should be doing from a cybersecurity best practices perspective. On the other hand, penetration testing helps answer the question “How effective would my cyber defenses be against a real-world attack?” Are the security controls you implemented working correctly or are there unseen vulnerabilities that leave your organization vulnerable to an attack?
We are often asked, what’s the difference between penetration testing and vulnerability scans. The easy answer is that vulnerability scans are an automated process and are the first step in determining whether or not your network has security gaps. Penetration testing takes things one step further by introducing the human element throughout the testing process. This approach helps eliminate false positive findings and is the best way to mimic a real-world attack by a skilled, patient hacker.

Actively Monitor Your Networks
Identify suspicious activity on your devices in real time
Next, active monitoring needs to be implemented to give you insight on whether or not a malicious actor is actively trying to compromise your network. Active monitoring helps answer the question, what is happening to my devices in real time, and is there suspicious activity that warrants further investigation?
As with all of these cybersecurity tips, this needs to be done proportionally and be based on the size or the organization. We aren’t asking you to spend your entire budget on a monitoring solution. At a minimum, you need to have some form of end-point or virus protection. This way, if a computer gets infected, the computer disconnects from the network and prevents the threat from spreading.
In addition to endpoint protection, are you collecting logs for everything? Having enhanced logging enabled and ensuring log data is saved for an extended period of time is crucial. Log data can prove invaluable for determining the facts surrounding a data breach.
Have a Written Incident Response Plan (IRP)
Make decisions ahead of time rather than in the midst of a crisis
A cornerstone of every cybersecurity strategy is the creation of an incident response plan (IRP). No one wants to find themselves without an IRP in the midst of a crisis. Thus, it is important to create your IRP when you have plenty of time on your hands and you can determine what steps you would take, who you would call, duties and responsibilities of staff and third parties, and the decision-making process, among other things.
So why is this so important? Companies tend to be scrutinized more for their actions post-breach than pre-breach. As such, be prepared for questions surrounding the incident, including investigating the incident, preservation of evidence, containment and remediation steps, identifying data and individuals who may be impacted, etc. Finally, make sure all of the items above are addressed in your incident response plan.
Understand Your Compliance Requirements
This is determined by the types of data you hold and your industry
The next issue that needs to be addressed is compliance requirements. It is important to know what your compliance obligations are and which laws apply to you. This can be done by looking at which types of data you have and the industry you’re in. All of these things will help make those determinations. Given the fact that you can be compliant but still not secure (and vice versa), we recommend regularly focusing on both elements.
Train Employees
Incorporate training during on-boarding and throughout the year
While this may seem like a given, we can’t say enough when it comes to training your employees. You’re only as strong as your weakest employee in their weakest moment. Things happen. We are all human, and we all make mistakes.
Incorporating security training during the employee on-boarding process as well as throughout the year is an excellent way to keep staff vigilant against attacks. There are many inexpensive security training solutions available that will provide your employees with information and tools on the latest threats and trends.
Perform a Data Audit
You can’t protect what you don’t know you have
We’ve already touched on compliance obligations and how you need to know what type of data you have. The importance behind a data audit and why it’s made it into the top ten list is that you can’t protect what you don’t know you have.
It is essential to understand what data is being stored on your systems as well as determining:
- Who owns it?
- Who is in charge of it?
- What’s it being used for?
- What is its sensitivity level?
- Does it require additional protections?
- Who has access to it?
- Where is it located?
Too often, companies maintain legacy data that is no longer necessary. Over time, that data, which could contain sensitive information, is forgotten if not audited regularly.
Perform an Account Audit
Identify unknown accounts or change in permissions more easily
Just as it’s important to audit your data, you should also regularly audit the accounts that have access to your data. Review all of the accounts that have access to your systems. Are they all known accounts? Should they all have the level of access that they’re currently granted? Are former employees still listed as active users? What other accounts should be deactivated?
Most importantly, reviewing and auditing accounts on a regular basis will allow you to identify whether or not an account has been created that doesn’t belong. Hackers often gain access to a system through a low level or unused account that should have been deleted.
From there, they can increase their administrative rights to take control of a company’s network. This is known as privilege escalation. Regularly auditing and monitoring accounts can help you identify anomalies like these before the hacker can grant themselves full access.
Initiate a Patch Management Program
Don’t rely on employees to patch their computers individually
Another issue that companies need to address is patch management. This is especially true for those with remote employees. If you’re not updating your operating systems, firmware to your IoT devices, applications that you use, and so on, you’re leaving yourself vulnerable. These patches are not just feature related, they are often security related.
Patches are being released on a periodic basis, and you need to have a program in place that addresses these. You can’t wait for your employees to update their machines individually. It’s too easy to say “remind me later” when the notification pops up, because you don’t want to interrupt what you’re doing in that moment. By implementing a company-wide patch management program, you can better protect your network from known threats.
Backup Data
Keep a copy offline and test your backups regularly
The last one of our cybersecurity tips that companies need to implement is a strong backup policy. Backing up your data is essential. But it’s not enough to just backup your data. It is important to ensure there is a copy stored offline, disconnected from your network to protect it from being included in an attack. Next, practice restoring your systems from backup to ensure no problems will arise in the event an actual restore is needed.
There have been instances where organizations go to pull data from their backups only to find that the data is corrupted or the backup simply doesn’t work. There are others who backed their data up into the cloud only to find out that it would take days, and sometimes weeks, to restore their files through downloads. Testing your backups also gives you an idea of how long your systems will be down in the event you do need to restore your data.
Next Steps
There you have it – the ten cybersecurity tips every SMB should be doing as a part of their cybersecurity strategy. If there is anything on this list your company is not currently doing, then we recommend adding it to your strategy moving forward.
Before you go, don’t forget to download the checklist by clicking on the image below! If you have a question regarding any of these cybersecurity tips, reach out by filling out the form to speak to one of our cybersecurity experts.